
Approach
Malware Identification
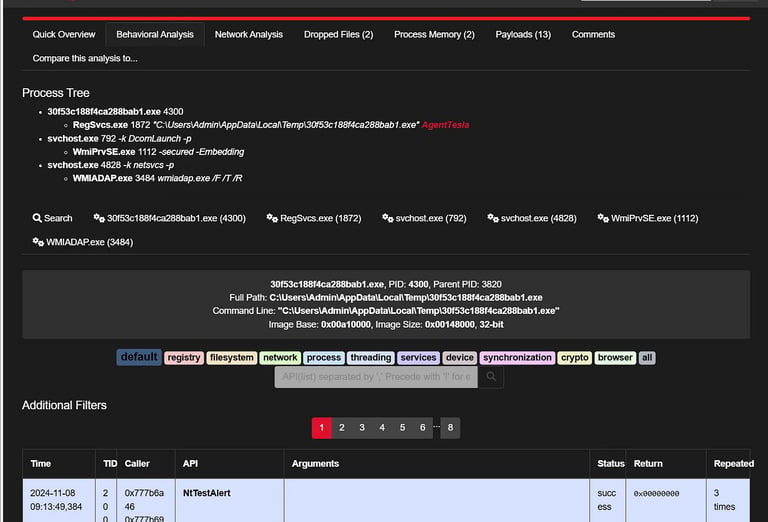
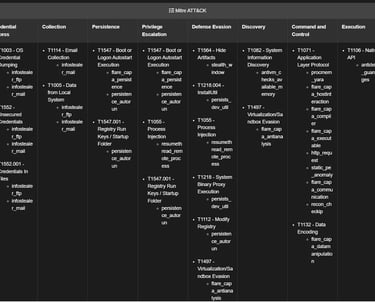
Detecting and categorizing malicious software through state-of-the-art techniques.Dynamic Analysis: Observing malware behavior in isolated environments to uncover its intent.
Static Analysis: Dissecting malware code to understand its functionality.
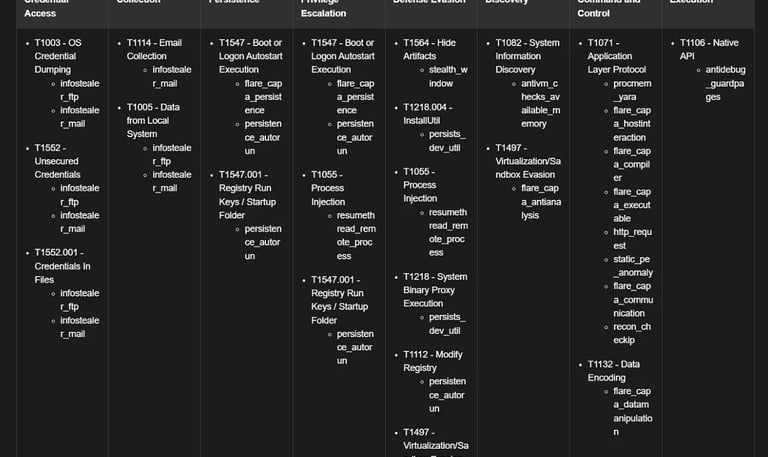
Indicators of Compromise (IoC) Extraction: Identifying signatures, file hashes, and artifacts for threat detection.
Behavioral and Impact Analysis
Assessing how malware interacts with systems to evaluate its potential damage.Behavioral Monitoring: Tracking system changes, file manipulations, and network activities.
Impact Assessment: Evaluating the risk and scope of infection to prioritize mitigation efforts.
Variant Analysis: Comparing against known malware families to understand evolutionary patterns.
Neutralization and Mitigation
Providing actionable solutions to eliminate malware and prevent future compromises.Remediation Guidance: Detailed steps to remove infections and restore systems.
Prevention Strategies: Recommendations for patching vulnerabilities and hardening defenses.
Tool Integration: Implementing detection mechanisms into your security infrastructure.
Features
With advanced tools and techniques, we identify Indicators of Compromise (IoCs), assess malware behavior, and provide actionable insights to neutralize threats and prevent future attacks. Each analysis is supported by detailed, customized reports to strengthen your organization's defenses effectively.




IoC Reporting: Comprehensive reports on artifacts and signatures for integration into threat intelligence systems.
Customized Solutions: Tailored strategies to address industry-specific malware threats.
Isolated Sandbox Environments: Safe testing of malware to observe its behavior without risk to your systems.
Advanced Tooling: Utilizing cutting-edge analysis frameworks and technologies.


