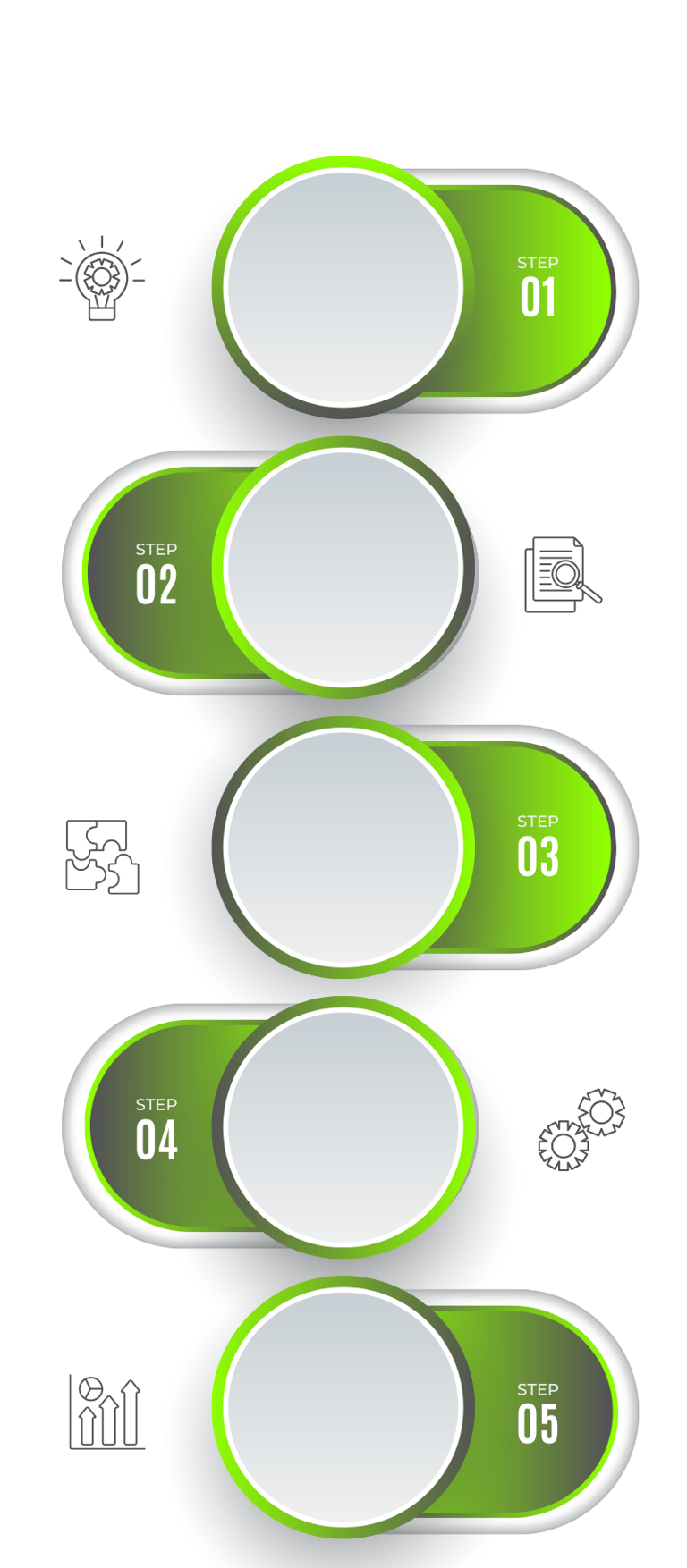
Reconnaissance
Scanning
Gaining Access
Maintaining Access
Clearing Tracks
Gathering critical information about the target environment using open-source intelligence (OSINT) and other advanced techniques. This step identifies potential entry points and weaknesses.
Mapping out the digital landscape through vulnerability scans and network analysis, pinpointing exploitable security gaps.
Exploiting vulnerabilities to infiltrate systems, mimicking real-world adversary tactics. This phase tests the effectiveness of your defensive measures.
Ensuring persistent access to compromised systems, replicating threat actor behavior to evaluate long-term risks and identify additional layers of security weaknesses.
Simulating the removal of evidence to assess how effectively your organization can detect, respond, and recover from an attack.
Proactive Risk Identification: Detect vulnerabilities before adversaries exploit them.
Realistic Attack Simulations: Test defenses against real-world threats to improve resilience.
Enhanced Threat Detection: Uncover hidden risks through advanced analysis.
Improved Incident Response: Strengthen response strategies with practical insights.
Regulatory Compliance: Ensure adherence to international standards and legal requirements.
Business Continuity Assurance: Minimize downtime and operational disruptions.
Resource Optimization: Allocate security investments more effectively.
Strategic Decision Support: Provide actionable insights for executive-level decision-making.
Holistic Security Integration: Bridge offensive and defensive strategies for comprehensive protection.
Reputation Protection: Build trust by demonstrating robust security measures.
The Offensive Edge: Unleashing the Benefits of Proactive Cybersecurity
Comprehensive Vulnerability and Risk Assessment
Advanced Adversary Simulation
Application and Infrastructure Security Testing
Attack Surface Management