Approach
How We Align the Pyramid with Our Services
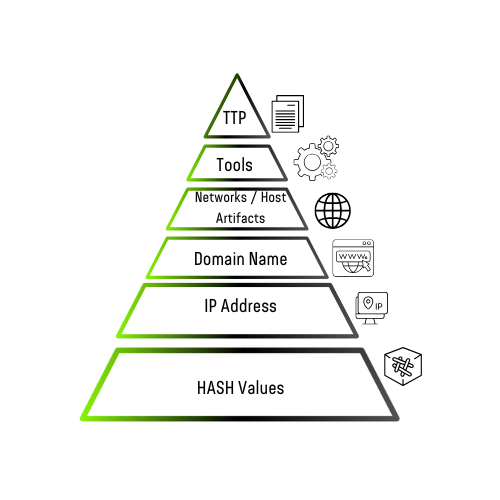
Our Threat Intelligence and Hunting services focus on proactive measures across all layers of the pyramid:
Automating the detection of simple IoCs like hashes, IPs, and domains.
Enhancing visibility and context through in-depth network and host analysis.
Neutralizing advanced threats by targeting adversary tools and TTPs.
Providing actionable intelligence to disrupt attacks at their most impactful levels.
By addressing each tier, we ensure that your organization’s defenses are comprehensive and robust, reducing adversary effectiveness at every step.
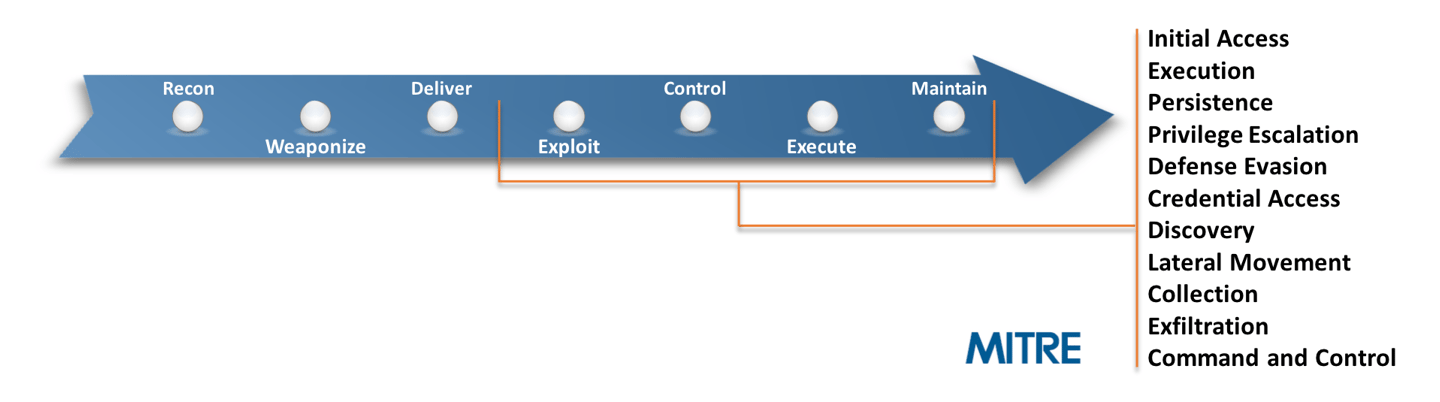
Proactively detect and neutralize threats at each phase of the Cyber Kill Chain. Leveraging frameworks like MITRE ATT&CK, we provide comprehensive protection to ensure your organization stays one step ahead of evolving cyber threats.
Proactive Prevention: Detect and neutralize threats before they cause harm.
Comprehensive Visibility: Gain a detailed understanding of your organization’s threat landscape.
Rapid Response: Minimize time between threat detection and mitigation.
Simplified Compliance: Alignment with industry standards and regulations.
Increased Efficiency: Reduce costs and effort with an automated and strategic approach.